In October, the Federal Bureau of Investigation issued a warning of increased targeting by ransomware operators of "big game"—targets with deep pockets and critical data that were more likely to pay ransoms to restore their systems. The past week has shown that warning was for good reason.
On November 18, a ransomware attack caused Louisiana's Office of Technology Services to shut down parts of its network, including the systems of several major state agencies. These included the governor's office, the Department of Health (including Medicare systems), the Department of Children and Family Services, the Department of Motor Vehicles, and the Department of Transportation. Louisiana Governor John Bel Edwards activated the state's cybersecurity response team.
Today, we activated the state's cybersecurity team in response to an attempted ransomware attack that is affecting some state servers. The Office of Technology Services identified a cybersecurity threat that affected some, but not all state servers. #lagov #lalege
— John Bel Edwards (@LouisianaGov) November 18, 2019
While some services have been brought back on line—in some cases, within hours—others are still in the process of being restored. Most of the interrupted services were because of "our aggressive actions to combat the attack," according to Louisiana Commissioner of Administration Jay Dardenne. "We are confident we did not have any lost data, and we appreciate the public's patience as we continue to bring services online over the next few days."
We will Ryuk you (or DopplelPaymer you)
The state did not pay the ransom demanded by attackers, who—based on the analysis of several researchers—were using a variant of the same Ryuk ransomware used in attacks on several Louisiana school districts' networks in July. That attack prompted Gov. Edwards to declare a state of emergency to allow for state agencies to assist local governments in their recovery from the attack. Ryuk attacks this summer also affected Georgia's court system and at least two Florida cities.
On November 15, the Charles-Nicolle University (CHU) Hospital in Rouen, France, was hit by ransomware that spread across five sites. The hospital was forced to shut down its networks to prevent the malware from spreading, according to a report from Le Monde, and staff were forced to use paper and pencil for tracking patients. While there were reports of a demand of a ransom payment of 1,500 euros for each of the over 6,000 computers affected at the hospital, a hospital spokesperson denied that a ransom demand had been made and said none would be paid. As of November 18, about 25% of the hospital's applications had been restored.
Also on November 15, the government of the Canadian territory of Nunavut suffered a ransomware outbreak that affected about 5,000 computers territory-wide. That attack, according to Nunavut government spokesperson Chris Puglia, used a variant of DoppelPaymer ransomware; the same malware hit Mexico's state-owned oil company PEMEX on November 12.
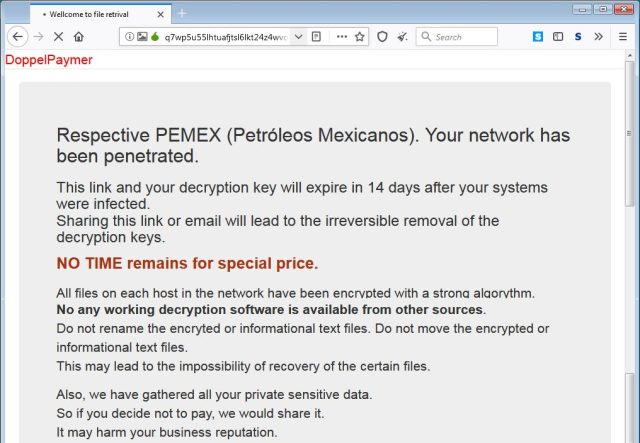
Despite documentation of the Pemex attack, company executives have continued to deny the company was affected.
#Pemex
reitera hacer caso omiso a boletines apócrifos que circulan en medios de información y redes sociales. Toda la información referente a la empresa productiva del Estado es publicada únicamente por vías institucionales y las redes oficiales.
— Petróleos Mexicanos (@Pemex) November 17, 2019
AccorRead More – Source







